As cyber threats continue to rise, utilizing a Raspberry Pi network security monitor has become an essential solution for safeguarding your digital infrastructure. Whether you're a home user, small business owner, or IT professional, understanding how to leverage Raspberry Pi for network security can significantly enhance your protection against malicious activities. In this comprehensive guide, we'll explore everything you need to know about setting up, configuring, and maintaining a Raspberry Pi-based network security monitoring system.
In today's interconnected world, network security is no longer a luxury but a necessity. With the increasing sophistication of cyberattacks, traditional security measures may fall short. This is where Raspberry Pi steps in as a cost-effective and powerful tool for monitoring network activities, identifying vulnerabilities, and mitigating potential threats.
This article will delve into the setup process, software options, best practices, and advanced techniques to ensure your Raspberry Pi network security monitor operates at its full potential. By the end, you'll be equipped with the knowledge and tools to protect your network effectively.
Read also:Caleb Goddard The Rising Star In The World Of Entertainment
Table of Contents
- Introduction to Raspberry Pi
- Why Use Raspberry Pi for Security?
- Hardware Setup for Raspberry Pi Network Security Monitor
Software Options for Network Monitoring
- Step-by-Step Installation Guide
Network Traffic Analysis with Raspberry Pi
- Essential Security Tools for Raspberry Pi
- Best Practices for Network Security Monitoring
Advanced Techniques for Threat Detection
- Common Issues and Troubleshooting
- Conclusion
Introduction to Raspberry Pi
Raspberry Pi is a compact, affordable, and versatile single-board computer that has revolutionized the way people approach technology. Designed primarily for educational purposes, it has quickly become a favorite among hobbyists, developers, and IT professionals alike. Its small form factor and low power consumption make it ideal for various applications, including home automation, media centers, and, most importantly, network security monitoring.
With its ability to run lightweight operating systems and support a wide range of software, Raspberry Pi serves as an excellent platform for building a dedicated network security monitor. By leveraging its capabilities, users can implement robust security measures to protect their networks from unauthorized access and malicious activities.
Why Use Raspberry Pi for Security?
Using Raspberry Pi for network security offers several advantages over traditional solutions:
- Cost-Effective: Raspberry Pi is significantly more affordable than commercial network security appliances, making it accessible to individuals and small businesses.
- Flexibility: Raspberry Pi supports a wide range of open-source software, allowing users to customize their security solutions based on specific needs.
- Energy-Efficient: Its low power consumption ensures it can run continuously without incurring high electricity costs.
- Community Support: A vast community of developers and enthusiasts provides extensive resources, tutorials, and support for Raspberry Pi projects.
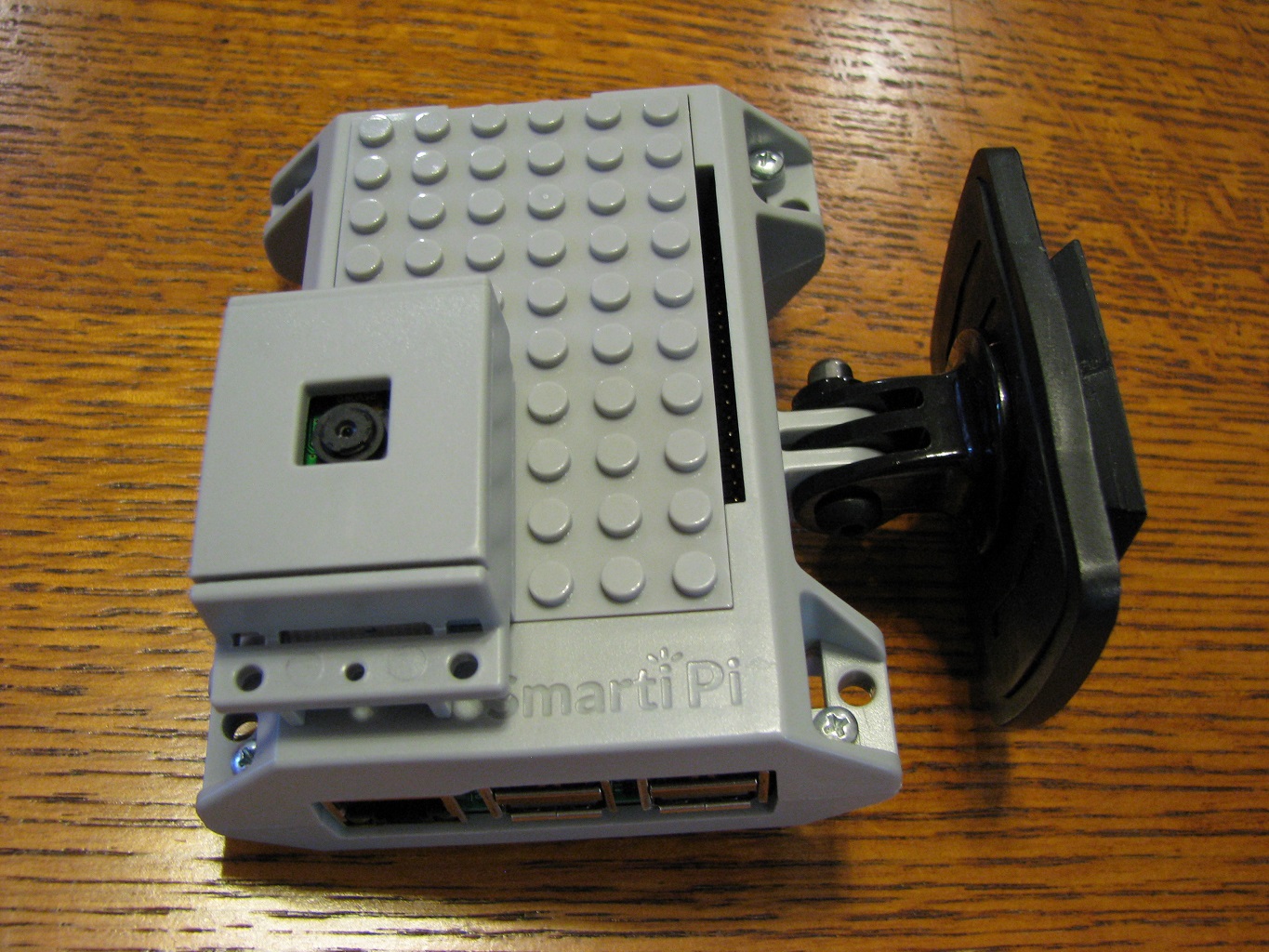
Hardware Setup for Raspberry Pi Network Security Monitor
Before diving into software configurations, it's crucial to set up the necessary hardware components for your Raspberry Pi network security monitor. Here's what you'll need:
- Raspberry Pi board (preferably Raspberry Pi 4 or later for better performance)
- MicroSD card with a minimum capacity of 16GB
- Power adapter compatible with your Raspberry Pi model
- Ethernet cable for connecting to your network
- USB Wi-Fi adapter (optional, for wireless monitoring)
- Case for Raspberry Pi (optional, for protection)
Once you've gathered all the components, follow these steps to assemble your Raspberry Pi:
- Insert the MicroSD card into the Raspberry Pi.
- Connect the Ethernet cable to your network switch or router.
- Attach any additional peripherals, such as USB Wi-Fi adapters.
- Plug in the power adapter to boot up the Raspberry Pi.
Software Options for Network Monitoring
Popular Software for Raspberry Pi Network Security Monitor
Several open-source software solutions are available for setting up a network security monitor on Raspberry Pi. Some of the most popular options include:
Read also:Rick Aviles The Untold Story Of A Visionary In The Tech World
- Kali Linux: A comprehensive penetration testing and security auditing distribution that offers a wide range of tools for network analysis and vulnerability assessment.
- Pi-hole: A network-wide ad blocker that also provides insights into DNS queries and potential threats.
- Snort: An intrusion detection and prevention system that can identify and block malicious network traffic.
- Wireshark: A powerful network protocol analyzer that allows you to capture and inspect packets in real-time.
Step-by-Step Installation Guide
Installing and configuring your Raspberry Pi network security monitor involves several steps. Below is a detailed guide to help you get started:
- Install the Operating System: Download the desired operating system image (e.g., Kali Linux or Raspbian) and flash it onto the MicroSD card using a tool like Balena Etcher.
- Configure Wi-Fi (Optional): If you plan to use wireless monitoring, edit the
wpa_supplicant.conffile to include your Wi-Fi network credentials. - Enable SSH: Create an empty file named
sshon the MicroSD card to enable SSH access for remote management. - Install Security Software: Use the package manager (e.g.,
apt) to install the necessary security tools on your Raspberry Pi. - Configure Monitoring Rules: Set up rules and filters to focus on specific types of network traffic or potential threats.
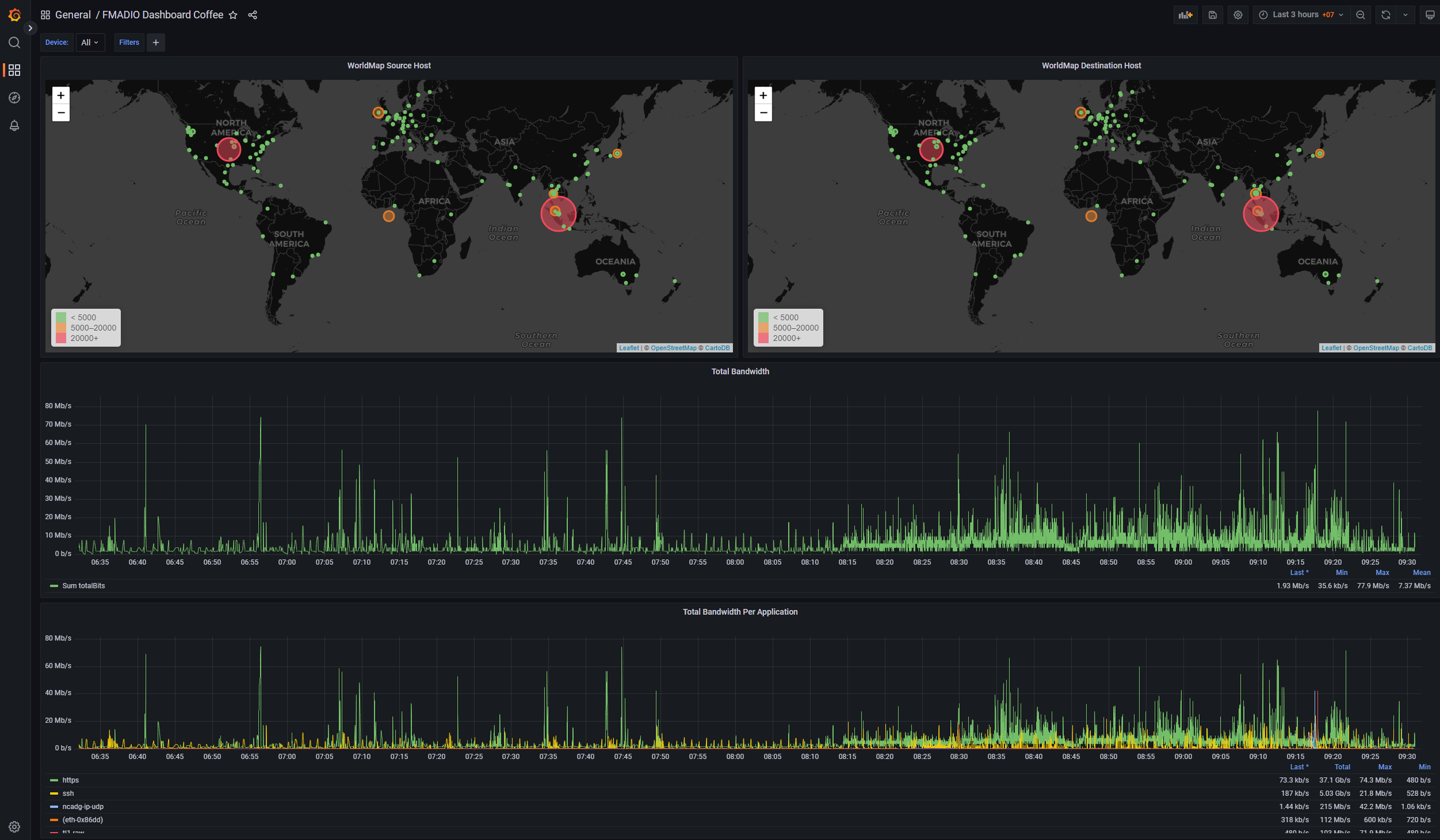
Network Traffic Analysis with Raspberry Pi
Understanding Network Traffic Patterns
Effective network security monitoring requires a thorough understanding of network traffic patterns. By analyzing incoming and outgoing data packets, you can identify anomalies that may indicate malicious activities. Key metrics to monitor include:
- Packet size and frequency
- Source and destination IP addresses
- Protocols used (e.g., HTTP, HTTPS, FTP)
- Unusual connection attempts
Tools like Wireshark and Snort can provide detailed insights into network traffic, helping you detect and respond to potential threats more effectively.
Essential Security Tools for Raspberry Pi
Equipping your Raspberry Pi network security monitor with the right tools is crucial for maximizing its effectiveness. Here are some essential tools to consider:
- Fail2Ban: Prevents brute-force attacks by automatically blocking IP addresses that exhibit suspicious behavior.
- ClamAV: A free antivirus engine for detecting and removing malware from your network.
- Nmap: A network exploration tool that can scan for open ports and identify vulnerabilities in connected devices.
- OSSEC: A host-based intrusion detection system that provides real-time alerts for security incidents.
Best Practices for Network Security Monitoring
To ensure your Raspberry Pi network security monitor operates optimally, follow these best practices:
- Regular Updates: Keep your operating system and security tools up to date to protect against newly discovered vulnerabilities.
- Secure Access: Use strong passwords and enable two-factor authentication for accessing your Raspberry Pi remotely.
- Log Analysis: Regularly review logs generated by your security tools to identify and investigate suspicious activities.
- Backup Configuration: Periodically back up your Raspberry Pi's configuration files to prevent data loss in case of hardware failure.
Advanced Techniques for Threat Detection
Implementing Machine Learning for Enhanced Security
For users seeking advanced threat detection capabilities, integrating machine learning into your Raspberry Pi network security monitor can yield significant benefits. Machine learning algorithms can analyze vast amounts of data to identify patterns and predict potential threats with higher accuracy. Popular machine learning frameworks like TensorFlow and Scikit-learn can be used to develop custom models tailored to your specific network environment.
Common Issues and Troubleshooting
While setting up and maintaining a Raspberry Pi network security monitor, you may encounter various issues. Here are some common problems and their solutions:
- Connection Issues: Ensure all cables are securely connected and check network settings for errors.
- Software Conflicts: Verify compatibility between installed software packages and resolve any conflicts by updating or reinstalling them.
- Performance Bottlenecks: Optimize your Raspberry Pi's configuration and allocate sufficient resources to handle network monitoring tasks.
Conclusion
Raspberry Pi network security monitor offers a powerful and cost-effective solution for enhancing your network's cybersecurity. By leveraging its capabilities and following best practices, you can effectively monitor network activities, identify vulnerabilities, and mitigate potential threats. Remember to stay updated with the latest security tools and techniques to ensure your Raspberry Pi remains a robust defense against cyberattacks.
We encourage you to share your experiences and insights in the comments section below. Additionally, don't hesitate to explore other articles on our site for more tips and tricks to improve your cybersecurity posture. Together, let's build a safer digital world!